TCP protocol: understanding what transmission control protocol is and how it works
Mar 14, 2024
/
Noviantika G.
/
5 min Read

Transmission Control Protocol (TCP) is the default data communication method between different devices over a network. It establishes and maintains a connection between the sender and the receiver during the transferring process.
With its mechanisms, TCP ensures that all packet data arrive unaltered. Moreover, it offers seamless and reliable transmission across various devices. It is used for email services and peer-to-peer sharing methods such as Secure Shell (SSH) and File Transfer Protocol (FTP).
This article will cover everything you need to know about TCP, how it works, and the differences between the stack and OSI models. Finally, we will compare the standard method and the User Datagram Protocol (UDP).
Download glossary for web beginners
What Is TCP?
TCP stands for Transmission Control Protocol and is used for transmitting data across networks. It breaks down the information into packets before sending them to the destination. With its advanced features, TCP offers a more reliable delivery system compared to other protocols.
How TCP Works
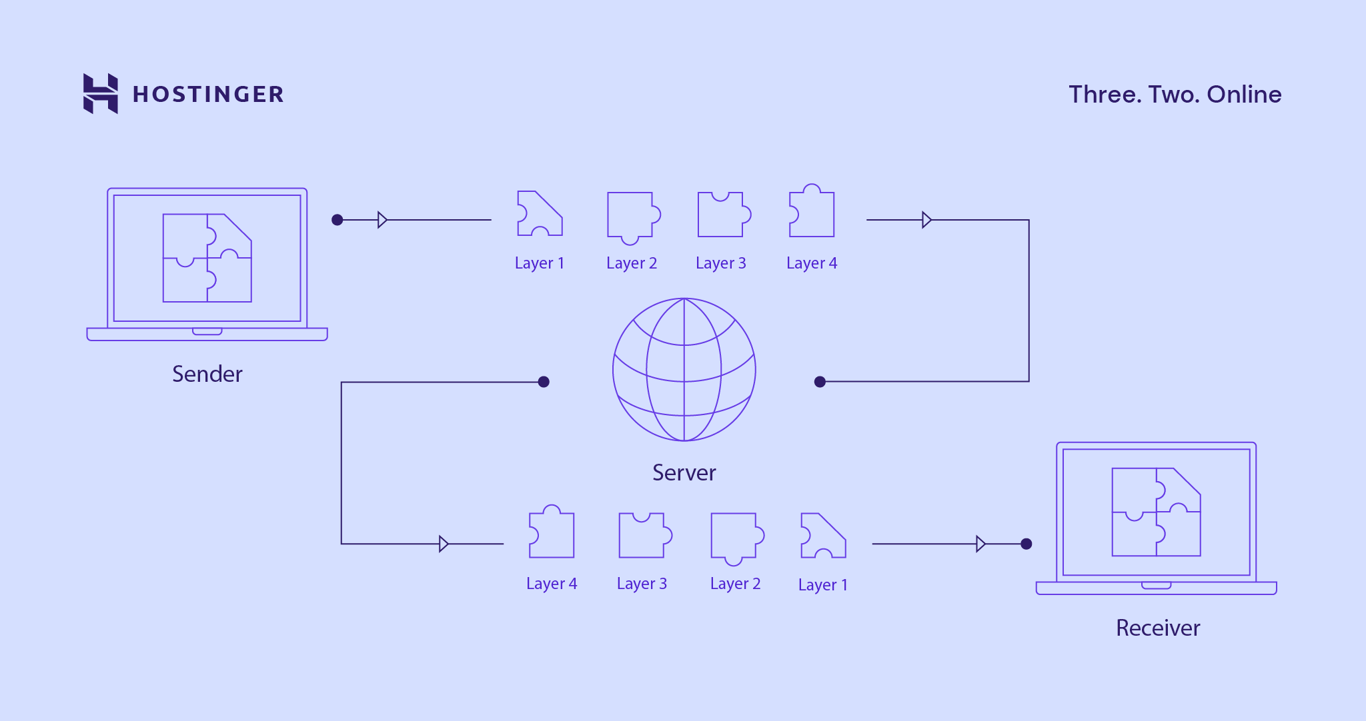
TCP breaks down data into packets and forwards them to the internet protocol (IP) layer to ensure each message reaches its destination computer. This helps prevent issues and maintain efficiency during the process.
Packets may travel along multiple routes if the actual path is congested or unavailable. Doing so will improve the network performance.
The internet protocol splits communication tasks into several layers, keeping the transmission process standardized. All packets will pass through at least four layers before reaching their destination.
The IP uses a three-way handshake method when creating the connection to ensure it can transfer several sockets in both directions concurrently.
However, the device and server must synchronize and acknowledge the packets before negotiating, separating, and transmitting the TCP sockets.
Suggested Reading
Then, TCP will go through the layers and reassemble the packets. Finally, the protocol will transmit the data to the receiving application.
During the process, TCP arranges the segment numbering system, handles lost packets, and manages flow control.
Why TCP Is Important
This high-level protocol is a core element in establishing regulations and standards for data transfers between multiple programs over networks. For web access, HTTP and HTTPS rely on the TCP connection.
Suggested Reading
What Is SSL? Understanding Secure Sockets Layer and How It Works
As a reliable protocol, it ensures communication occurs consistently, regardless of the devices and locations. Furthermore, it protects data delivery with advanced controls, such as acknowledgments and congestion avoidance mechanisms.
Aside from being non-proprietary, TCP also allows and accommodates new protocols.
The TCP Stack Model
The TCP stack model contains four layers:
- Application layer. Establishes the connection between the application and data. It also opens access to multiple network resources.
- Transport layer. Creates TCP connections and determines how much data to send.
- Internet layer. Sends IP packets to the actual destination using various networks.
- Link or network interface layer. Controls the physical messaging and media for data transmission.
When passing each TCP layer, data will be repackaged based on its transport protocols and functionality.
Requests pass down to the web server via the stack and start at the application layer as data. The system will divide the information into different packet types at each stage. The data will then move to the transport layer, which will be classified into TCP segments.
The next step is transmitting them to the internet layer, where they will become datagrams. The packets will move to the network layer to create a TCP segment. Once the web server replies, the data will move upward via the stack to reach the application layer in the original format.
The OSI Model
While the TCP stack model frames the data by protocol usage, Open System Interconnection (OSI) is a conceptual method based on the network communication type.
The OSI model consists of seven layers:
- Application layer. Enables software to send, receive, and present comprehensible information to users.
- Presentation layer. Encrypts the information and ensures the data is in a readable format.
- Session layer. Manages the connections and controls ports along with sessions.
- Transport layer. Transfers data via transmission protocols such as TCP and UDP.
- Network layer. Defines the packets’ routing and physical path.
- Data Link layer. Determines the data format on the network and checks for errors.
- Physical layer. Transfers bit streams through the physical medium.
The OSI method moves the data down, with each layer adding information. Once they reach the last stage, they will be transmitted over the network.
TCP vs UDP
UDP is an alternative to TCP, offering different ways to communicate network traffic. While the former ensures reliable transfers, the latter prioritizes efficiency and speed. Here are six common differences between TCP and UDP:
- The service type. TCP is a connection-based protocol that requires the communicating devices to connect before transferring the actual data. In comparison, UDP is a connectionless protocol that transmits information without checking whether the receiver can accept the signal.
- Error-checking mechanisms. TCP provides extensive error-detection procedures, such as determining the connection timeout period, providing a checksum field, and receiving and sending acknowledgments. On the other hand, UDP only performs basic problem-checking using checksums.
- Sequence. In TCP, packets arrive in a specific order at the receiver. While in UDP, the system sends independent packets without sequence numbers.
- Data retransmission. TCP will resend any lost or corrupted packets, while UDP won’t.
- Flow control mechanism. TCP uses this technique to calibrate the data transfer speed and limit the rate when a sender transfers data. UDP doesn’t have a flow control mechanism.
- Stream types. TCP interprets data as bytes and transmits the IP packet to segment boundaries. In contrast, UDP reads data as messages that contain bundles.
- Header length. A TCP header ranges from 20-60 bytes, while UDP is eight fixed-length bytes.

Conclusion
Transmission Control Protocol (TCP) is a standard protocol for sending data and messages across networks, offering reliable services and advanced mechanisms. TCP defines how to connect multiple computers or application programs and ensures secure data transmission between them.
The TCP stack model uses four layers to transfer data – application, transport, internet, and network. On the other hand, the OSI model provides seven stages – application, presentation, session, transport, network, data link, and physical.
Here are three major differences between TCP and UDP:
- TCP is a connection-oriented protocol, while UDP is a connectionless protocol.
- TCP offers extensive error-checking procedures. In comparison, UDP only performs basic fault-monitoring mechanisms.
- TCP sends data packets in a specific order, while UDP doesn’t.
We hope this article has helped you learn more about TCP. If you have any questions or suggestions, please leave them in the comments section below.
Suggested Readings
How to Fix “Your Connection Is Not Private” Error
This Site Can’t Provide a Secure Connection Error
How to Fix ERR_SSL_VERSION_OR_CIPHER_MISMATCH
NET::ERR_CERT_COMMON_NAME_INVALID Error
Transmission Control Protocol FAQ
In this section, we will answer frequently asked questions about TCP.
What Is the Difference Between TCP and IP?
TCP and IP are two core components of the internet protocol suite. While the former securely transfers and routes data via the network architecture, the latter defines the IP address.
The TCP/IP model consists of several protocols, such as Internet Control Message Protocol (ICMP) and Address Resolution Protocol (ARP).
What Are TCP Ports?
A TCP port consists of 16-bit unsigned integers. The Internet Assigned Numbers Authority (IANA) maintains port number assignments for different uses.
Currently, TCP ports are 65,535 in total, including port 21 for FTP, port 110 for Post Office Protocol (POP), and port 143 for Internet Message Access Protocol (IMAP).
All of the tutorial content on this website is subject to Hostinger's rigorous editorial standards and values.